Planning a wedding brings excitement, but sharing guest information digitally often triggers privacy concerns. You worry about email addresses falling into the wrong hands or personal details being misused. Modern digital wedding invitations have evolved to address these fears head-on, incorporating sophisticated security measures that actually protect your guests better than traditional paper methods. This guide reveals how privacy-focused digital invitations work, what protections you should expect, and practical steps to safeguard everyone's information while streamlining your event management.
Table of Contents
- Why Privacy Concerns Arise With Digital Wedding Invitations
- Core Privacy Protections In Digital Invitations
- Comparing Privacy-Focused Digital Invitation Features
- Practical Tips For Protecting Privacy With Digital Wedding Invitations
- Explore Privacy-Focused Digital Wedding Invitations With The Digital Yes
- FAQ About How Digital Invitations Protect Privacy
Key takeaways
| Point | Details |
|---|---|
| Secure token links | Random tokens in URLs prevent unauthorized access and can expire automatically after your event |
| Minimal data collection | Privacy-first platforms request only essential guest information, reducing exposure risks significantly |
| Calendar security | Disabling automatic calendar processing prevents metadata leaks that could compromise attendee privacy |
| No account requirement | Guests access invitations without creating profiles, eliminating unnecessary data storage and breach risks |
| Transparent consent | Clear opt-in processes and data usage policies build trust while complying with privacy regulations |
Why privacy concerns arise with digital wedding invitations
Many couples hesitate to embrace digital invitations because they fear exposing guest email addresses to spam or data breaches. Traditional email invitations can indeed create vulnerabilities when sent through unsecured channels or when recipient lists become visible to all attendees. These concerns are valid but often stem from outdated practices rather than modern digital invitation technology.
Calendar invitation files present a particularly sneaky risk. When you send .ics files, they contain metadata about your event and attendee list. If guests have automatic calendar processing enabled, these files can leak attendee information without anyone's explicit consent. The problem intensifies when calendar apps sync across multiple devices and cloud services, multiplying the points where data could be intercepted or misused.
Some people assume digital invitations require guests to create accounts on unfamiliar platforms, raising legitimate access and data storage concerns. Others worry about their personal information being sold to third parties or used for marketing purposes beyond the wedding context. These misconceptions often prevent couples from exploring bespoke digital invitations that could actually enhance their planning experience.
The reality is more nuanced than blanket fears suggest:
- Guest email addresses can be protected through secure distribution methods
- Modern platforms offer privacy controls that paper invitations never could
- Data collection can be limited to only what you need for event management
- Transparent policies let guests understand exactly how their information gets used
Understanding these specific risks helps you evaluate digital invitation options critically. Not all platforms handle privacy equally, so knowing what threats exist prepares you to ask the right questions and choose solutions that genuinely protect your guests while delivering the convenience and features you want for your special day.
Core privacy protections in digital invitations
The most effective digital invitations use secure shareable links with random tokens instead of simple URLs anyone could guess. These tokens function like unique keys, with each invitation link containing a long string of random characters that would be virtually impossible to discover through trial and error. Better yet, these links can expire automatically after your RSVP deadline or wedding date, ensuring that access remains tightly controlled even if someone forwards the invitation inappropriately.

Account-free access represents another crucial protection. When guests can view and respond to invitations without creating usernames, passwords, or profiles, you eliminate an entire category of privacy risks. No stored credentials means no password breaches, no forgotten login hassles, and no personal data sitting in databases long after your wedding concludes. This approach respects your guests' time while protecting their information.
Disabling automatic calendar processing prevents the metadata leaks that plague traditional calendar invitations. Privacy-focused platforms either avoid .ics files entirely or provide them with minimal metadata and clear instructions for manual import. This small technical choice makes a significant difference in preventing unintended data exposure across synced devices and cloud services.
Data minimization principles guide what information gets collected:
- Request only names and RSVP responses for basic invitations
- Add meal preferences or plus-one details only when operationally necessary
- Make phone numbers and addresses optional unless required for specific logistics
- Provide clear explanations for why each data field is requested
- Offer guests control over what they share and how it gets used
Transparent consent processes build trust while meeting legal requirements. Quality platforms display privacy policies in plain language, not legal jargon, and obtain explicit opt-ins before collecting any information beyond the absolute minimum. You should see checkboxes for optional data sharing, not pre-checked boxes that assume consent.
Pro Tip: Look for platforms that conduct regular security audits and publish their privacy practices openly. If a provider won't clearly explain how they protect guest data, that's a red flag worth heeding.
Privacy-first design extends beyond technical measures to include thoughtful user experience choices. For example, effective wedding RSVP tracking systems let you manage responses without exposing guest lists to other attendees or requiring guests to navigate complex interfaces that might inadvertently reveal others' information. The best solutions make privacy protection invisible to users while maintaining robust safeguards behind the scenes.
Comparing privacy-focused digital invitation features
Token-based link security offers substantial advantages over traditional password protection. Passwords require guests to remember or store credentials, creating friction and potential security weaknesses if people choose simple passwords or reuse them across sites. Token links work immediately without any guest action, yet provide comparable or superior security through cryptographic randomness and controlled distribution.
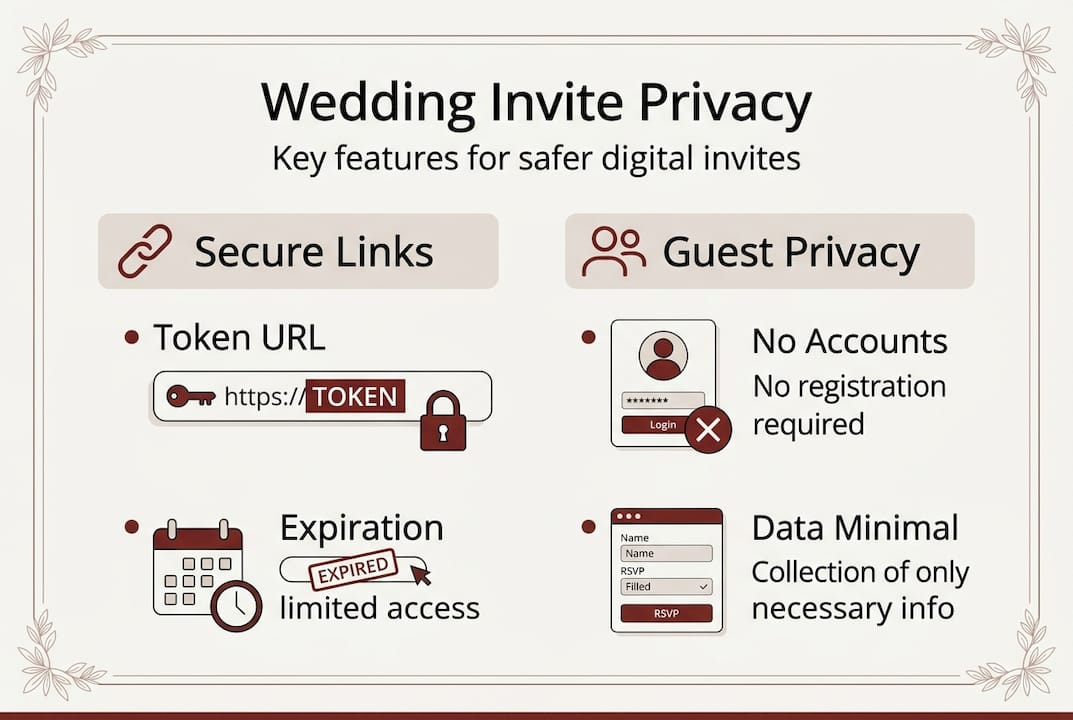
Data collection philosophies vary dramatically across platforms. Some services request extensive guest profiles including birthdays, social media handles, and detailed preferences that extend far beyond wedding logistics. Others practice radical minimalism, collecting only what's operationally necessary for event management. The data minimization approach significantly reduces privacy risks by limiting what could potentially be exposed in a breach or misused.
| Feature | Privacy-Focused Approach | Traditional Approach | Privacy Impact |
|---|---|---|---|
| Link Access | Random token URLs that expire | Simple URLs or password protection | High: tokens prevent unauthorized discovery |
| Guest Accounts | No registration required | Account creation mandatory | High: eliminates credential storage risks |
| Data Collection | Minimal: name and RSVP only | Extensive profiles and preferences | Medium: less data means less exposure |
| Calendar Integration | Manual import with minimal metadata | Automatic .ics processing | Medium: prevents metadata leaks |
| Consent Process | Explicit opt-in with clear explanations | Pre-checked boxes or assumed consent | Low: transparency builds trust |
Automatic calendar integration presents a classic convenience versus privacy tradeoff. While guests appreciate having events automatically added to their calendars, this process can expose attendee lists and event details across multiple synced devices and services. Privacy-conscious platforms either skip automatic integration entirely or provide it with robust warnings and minimal metadata inclusion.
Expiration dates and no-account requirements work together to create a security-by-design approach. When invitation links automatically become invalid after your event, you eliminate the risk of old links being discovered and exploited months or years later. Combined with account-free access, this means zero long-term data retention and no ongoing security obligations for either you or your guests.
Pro Tip: Test your chosen platform by sending yourself an invitation and examining exactly what information it requests and how the process feels from a guest perspective. This hands-on evaluation reveals privacy practices more clearly than any marketing description.
Best practices for wedding planners and couples include verifying that your platform provides transparent privacy policies, offers guests control over their information, limits data collection to operational necessities, and implements technical safeguards like token-based access. When evaluating premium wedding invitation features, prioritize those that enhance your event without compromising guest privacy.
Practical tips for protecting privacy with digital wedding invitations
Start by instructing guests to disable automatic calendar adding if your invitation includes calendar files. Most email and calendar applications let users turn off automatic processing, requiring manual review before adding events. This simple step prevents metadata leaks and phishing risks associated with automatic calendar integration. Include clear instructions in your invitation email so guests know how to protect themselves.
Verify that your invitation links expire automatically after your RSVP deadline or wedding date. Test this by creating a sample invitation and checking whether the link still works after the expiration time. Expired links protect you from unauthorized access if someone discovers an old invitation months later or if a guest accidentally forwards the link to unintended recipients.
Limit your data collection ruthlessly. Before requesting any information beyond names and RSVP status, ask yourself whether you genuinely need it for event logistics:
- Meal preferences: necessary only if you're providing dinner with options
- Phone numbers: useful for day-of coordination but often optional
- Addresses: required only if you're sending physical items or thank-you notes
- Dietary restrictions: essential for catering but can be collected separately
- Plus-one details: needed for accurate headcounts but keep fields minimal
Choose platforms that never require guests to create accounts. This single criterion eliminates numerous privacy risks while respecting your guests' time. Account-free systems mean no passwords to remember, no profiles to manage, and no personal data lingering in databases after your wedding concludes. The convenience benefits guests while the privacy benefits protect everyone involved.
Pro Tip: Create a simple privacy statement for your wedding website or invitation page explaining how you'll use guest information and confirming you won't share it with third parties. This transparency builds trust and demonstrates your commitment to protecting their privacy.
Regularly review your invitation platform's privacy settings, especially if you set up your invitations months before your wedding. Platform policies and features can change, so periodic checks ensure your privacy protections remain active and effective. Look for any new data collection requests or changed default settings that might affect guest privacy.
When organizing wedding guest responses, use features that aggregate data without exposing individual guest information unnecessarily. For example, view total RSVP counts and meal preference summaries rather than sharing complete guest lists with vendors or wedding party members who only need aggregate numbers for planning purposes. This compartmentalized approach limits information exposure while still enabling effective coordination.
Explore privacy-focused digital wedding invitations with The Digital Yes
Modern wedding planning demands solutions that balance convenience with genuine privacy protection. The Digital Yes delivers exactly this combination through secure, token-based digital invitations designed specifically for privacy-conscious couples and professional wedding planners. Every invitation uses cryptographically random URLs that expire automatically, ensuring your guest information stays protected throughout your planning process and beyond.
The platform collects only the minimal personal data necessary for effective event management, with transparent consent processes that respect your guests' privacy preferences. Built-in RSVP tracking streamlines guest management without requiring accounts or unnecessary data collection, while real-time updates keep you informed without compromising security. Whether you're planning an intimate celebration or coordinating a large event as a professional planner, The Digital Yes combines cutting-edge privacy protections with the elegant, customizable designs that make your wedding invitations memorable for all the right reasons.
FAQ about how digital invitations protect privacy
Are digital invitations really safer than paper invitations?
Digital invitations can be significantly safer when designed with privacy-first principles like token-based access, data minimization, and expiration dates. Paper invitations expose addresses through postal delivery and provide no control over who sees them after arrival. Modern digital platforms offer granular access controls and automatic expiration that paper simply cannot match.
How can guests protect their privacy when accepting digital invites?
Guests should disable automatic calendar processing in their email and calendar apps to prevent metadata leaks. They should also avoid creating accounts on invitation platforms when possible, review what information they're sharing before submitting RSVPs, and never forward invitation links without the couple's explicit permission since tokens grant access to anyone who has them.
What data do digital invitation platforms usually require?
Privacy-focused platforms require only names and RSVP responses for basic functionality. Additional optional fields might include meal preferences, plus-one details, or dietary restrictions when operationally necessary. Quality platforms clearly explain why each data field is requested and make non-essential information optional rather than mandatory.
Can automatic calendar adding be fully disabled for invites?
Yes, most email clients and calendar applications allow users to disable automatic processing of calendar invitation files. This setting prevents .ics files from automatically adding events to calendars without user review. Couples can also choose platforms that avoid automatic calendar integration entirely or provide manual import options instead.
How do expiration links improve invitation security?
Expiration links automatically become invalid after a specified date, typically your RSVP deadline or wedding date. This time-limited access prevents old invitation links from being discovered and used months or years later. If someone finds or receives a forwarded invitation after expiration, they cannot access your event details or guest information, significantly reducing long-term security risks.
